Integration with Sentry
Arcadia Enterprise integrates with Sentry.
To integrate the Arcadia Visualization server with a Sentry-enabled Hadoop system, you must perform the following tasks:
-
Check the Enable Impersonation box in the connection setup. This directs the system to include the connected ArcViz username as part of each request made to the database. The system uses this username to authorize access to databases and tables named in the request.
-
Configure the site-local parameters on ArcViz to enable connection to the Sentry system, as provided by the
settings.pyconfiguration file.
When you enable a Sentry connection, the system mirrors the roles and group memberships from the Sentry system. This synchronization enables full access to the datasets (and dashboards built on those datasets) to all users with defined Sentry roles and group memberships.
Arcadia stores the group memberships for a roles mirrored from Sentry in a separate
sentry_groups field of a role definition. If this field exists, the system
does not allow the addition of other users or groups to the role membership. All Sentry role
membership must be managed from the Sentry system.
ArcViz mirrors and maintains role definitions from Sentry through periodic polling of the Sentry system, with frequency defined through site settings. If during a polling cycle, the system determines that a role formerly imported from Sentry no longer exists, it empties the sentry groups membership field for that role. This inactivates the role, but preserves the potentially extensive privilege structure assigned to it.
Integration with LDAP
LDAP integration consists of the following steps:
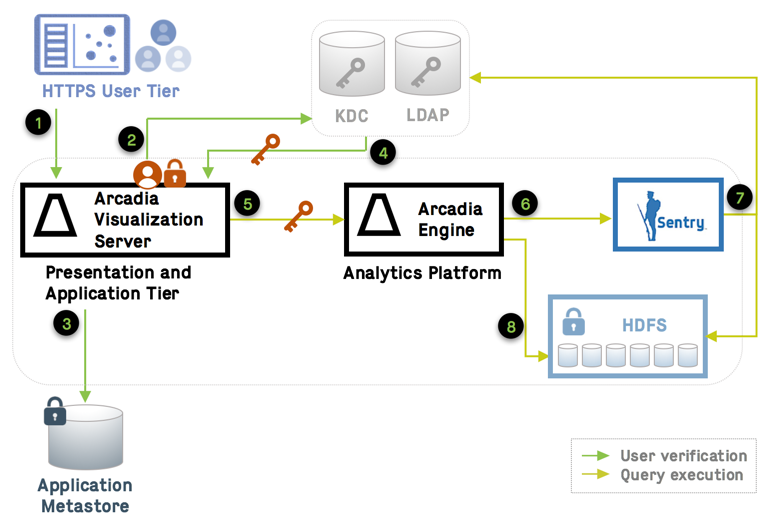
- Users initiate access to the application layer through an SSL-enabled connection protocol.
- The system checks user credentials against LDAP. When valid, the user obtains the group membership information, and successfully logs into Arcadia.
- The first time the user logs in, Arcadia adds the username in the application metastore. In subsequent user sessions, the system references this user information.
- Arcadia establishes domain trust at the Kerberos level, using the service principal account. This account is renewed periodically.
- During query execution, Arcadia uses the Kerberos ticket and proxy user privileges to communicate between Arcadia Engine and Arcadia Visualization Server.
- The system checks against Sentry, using impersonation for data authorization.
- Sentry synchronizes with LDAP users and user groups, and databases.
- Arcadia Engine reads HDFS blocks securely, by checking against Sentry.
Integration with RBAC
Arcadia Data's Role Based Access Control framework (RBAC) provides access control over connections and datasets. See Role Based Access Control.
RBAC integrates with existing security systems such as Kerberos/LDAP, Sentry, and Ranger, and takes advantage of other tools for external user and group specification, password management, table- and column-level access, and so on.
Integration with Sentry and/or LDAP enables the following combinations of access control:
| Access Control Protocols | Users | Groups | Roles | Role-Group Mapping |
|---|---|---|---|---|
| Sentry and LDAP | LDAP, internal | LDAP, external | Sentry, internal | Sentry, internal |
| Local and LDAP | LDAP, internal | LDAP, external | local | local |
| Local and Sentry | local | local | Sentry, internal | Sentry, internal |
| Local | local | local | local | local |
where:
- local: controls provided in the Arcadia Visualization server
- internal: information from the object in the external system used with objects created in ArcViz
- external: external objects only mirrored or cached for use by ArcViz
Consider the first case, with both Sentry and LDAP.
- Users
The system makes a copy of the user's information to create a user account within ArcViz. It does not store the password, so the account cannot be used without an LDAP connection. Subsequent changes to account information made through the LDAP interface, such as name change, are not picked up by ArcViz.
- Groups
The system always references LDAP for group membership definitions.